





Jump In iam pandoraaa leaks signature webcast. Pay-free subscription on our cinema hub. Immerse yourself in a great variety of films featured in flawless visuals, the ultimate choice for high-quality viewing enthusiasts. With the newest additions, you’ll always remain up-to-date. Witness iam pandoraaa leaks personalized streaming in amazing clarity for a highly fascinating experience. Sign up for our community today to view VIP high-quality content with zero payment required, no sign-up needed. Experience new uploads regularly and investigate a universe of one-of-a-kind creator videos perfect for prime media followers. Seize the opportunity for unseen videos—swiftly save now! Witness the ultimate iam pandoraaa leaks singular artist creations with impeccable sharpness and select recommendations.
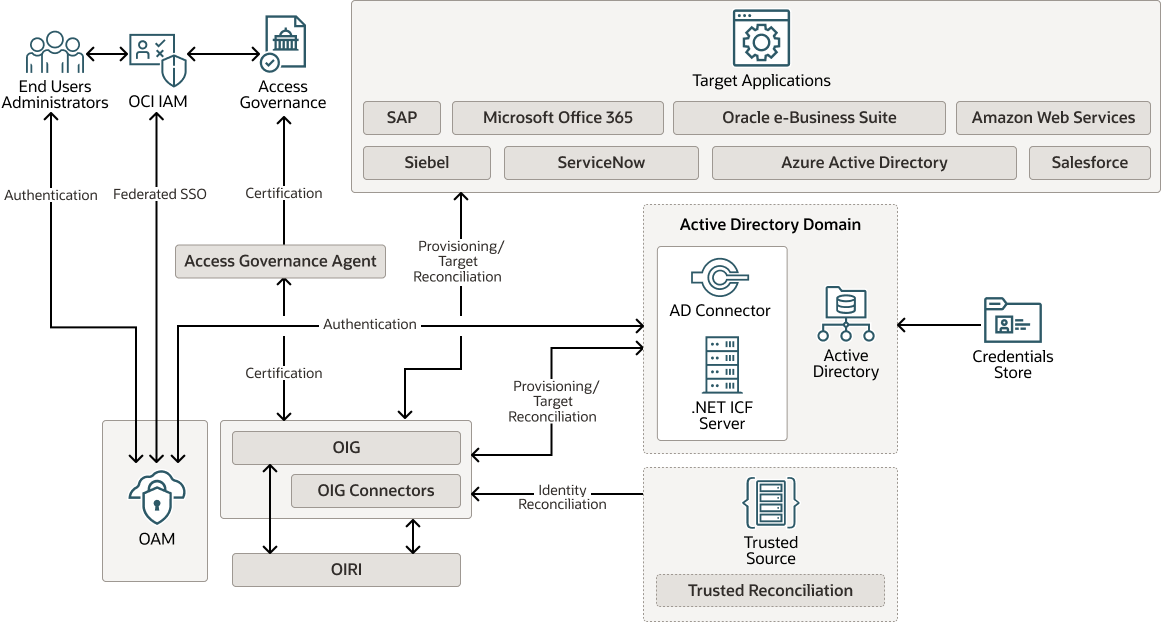
Learn about aws identity and access management (iam), its features, and basic concepts. Iam is a framework of policies, technologies, and processes that ensures the right individuals have access to the right resources at the right time and for the right reasons Identity management, otherwise known as identity and access management (iam) is an identity security framework that works to authenticate and authorize user access to resources such as applications, data, systems, and cloud platforms. Identity and access management (iam) is the cybersecurity discipline that deals with provisioning and protecting digital identities and user access permissions in an it system
Iam tools help ensure that the right people can access the right resources for the right reasons at the right time. Identity and access management is a fundamental and critical cybersecurity capability Simply put, with its focus on foundational and applied research and standards, nist seeks to ensure the right people and things have the right access to the right resources at the right time. Identity and access management (iam) is a framework that allows the it team to control access to systems, networks and assets based on each user’s identity.

Conclusion and Final Review for the 2026 Premium Collection: Finalizing our review, there is no better platform today to download the verified iam pandoraaa leaks collection with a 100% guarantee of fast downloads and high-quality visual fidelity. Seize the moment and explore our vast digital library immediately to find iam pandoraaa leaks on the most trusted 2026 streaming platform available online today. We are constantly updating our database, so make sure to check back daily for the latest premium media and exclusive artist submissions. Start your premium experience today!